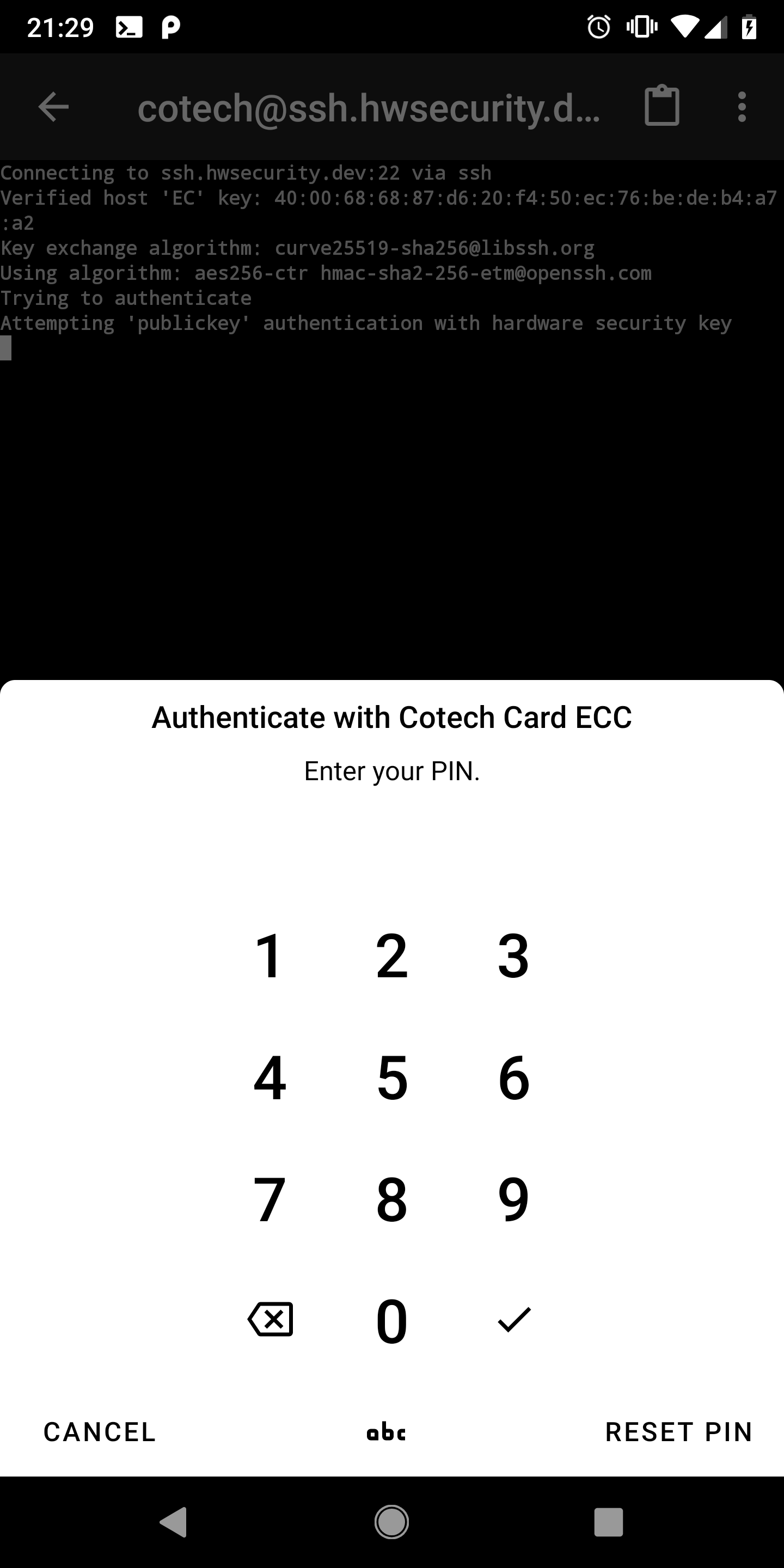
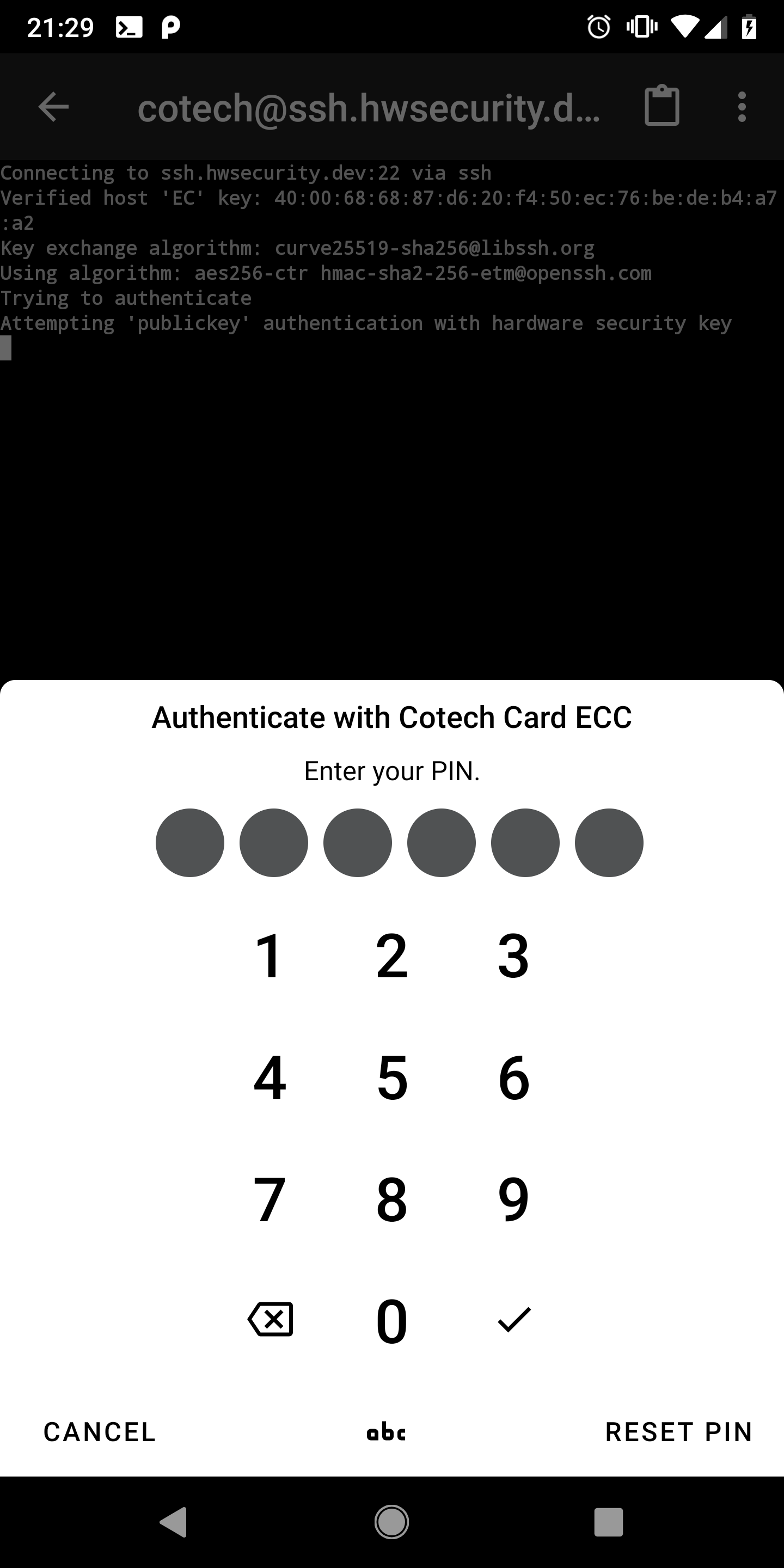
You can switch to a keyboard input by clicking the small button with “abc” at the bottom of the dialog.
However, we recommend a numeric PIN as there is no need to choose a difficult and long PIN with other characters.
Security Keys and Smartcards have a vastly different threat model than password-encrypted files or Internet accounts.
While the latter can be brute-forced by trying all possible combinations of different password-lengths, security keys and smartcards get locked after 3 failed PIN attempts.
Then, the card needs to be unlocked again using the PUK (also called Admin-PIN).
After 3 failed attempts using the PUK, the card is finally blocked and can only be resetted completely.
Thus, even when choosing a short numeric PIN (the standard recommends 6 digits), the probability that an attacker can guess the correct PIN is negligible low.